Automated Attendance And Student Productivity
Link to open source: https://github.com/shoil-abbas/RedOps
it is useful because it works on minimal cost and provide no fake attendence Server-signed attestation is extremely useful for individuals, organizations, and digital platforms because it creates a strong layer of trust in communication, transactions, and authentication processes. In today’s world, where cyberattacks, identity theft, and app tampering are common, simply relying on usernames, passwords, or basic validations is not enough. Server-signed attestation provides cryptographic proof that the information, device, or software involved is genuine and has not been altered. For example, when a mobile app uses Firebase App Check or Google Play Integrity, the server can sign an attestation response that confirms the app is authentic, running on a trusted device, and not being manipulated by attackers. This gives confidence to businesses that their services are not being accessed by bots, malware, or modified applications. Similarly, in hardware-level security, trusted execution environments (such as TPM or Intel SGX) use attestation to prove that the device is in a secure state before sensitive operations like payments, data decryption, or login sessions are allowed. From a user’s perspective, this means their private information, such as banking credentials, health records, or personal chats, remain safe from interception or misuse. For service providers, it reduces fraud, protects revenue, and ensures that only verified clients are accessing their systems. Even in identity verification systems like WebAuthn or FIDO2, attestation signed by a server makes sure that authentication devices like security keys or biometrics are legitimate, not fake clones. Beyond security, this technology also saves time and resources because automated verification through server-signed attestation is faster and more reliable than manual checks. Overall, it benefits others by establishing digital trust, improving safety for users, protecting organizations against malicious actors, and enabling secure ecosystems where people can confidently use online services, knowing that the server has already validated and signed the authenticity of devices, apps, and data being exchanged.
This build was uploaded as a hackathon project
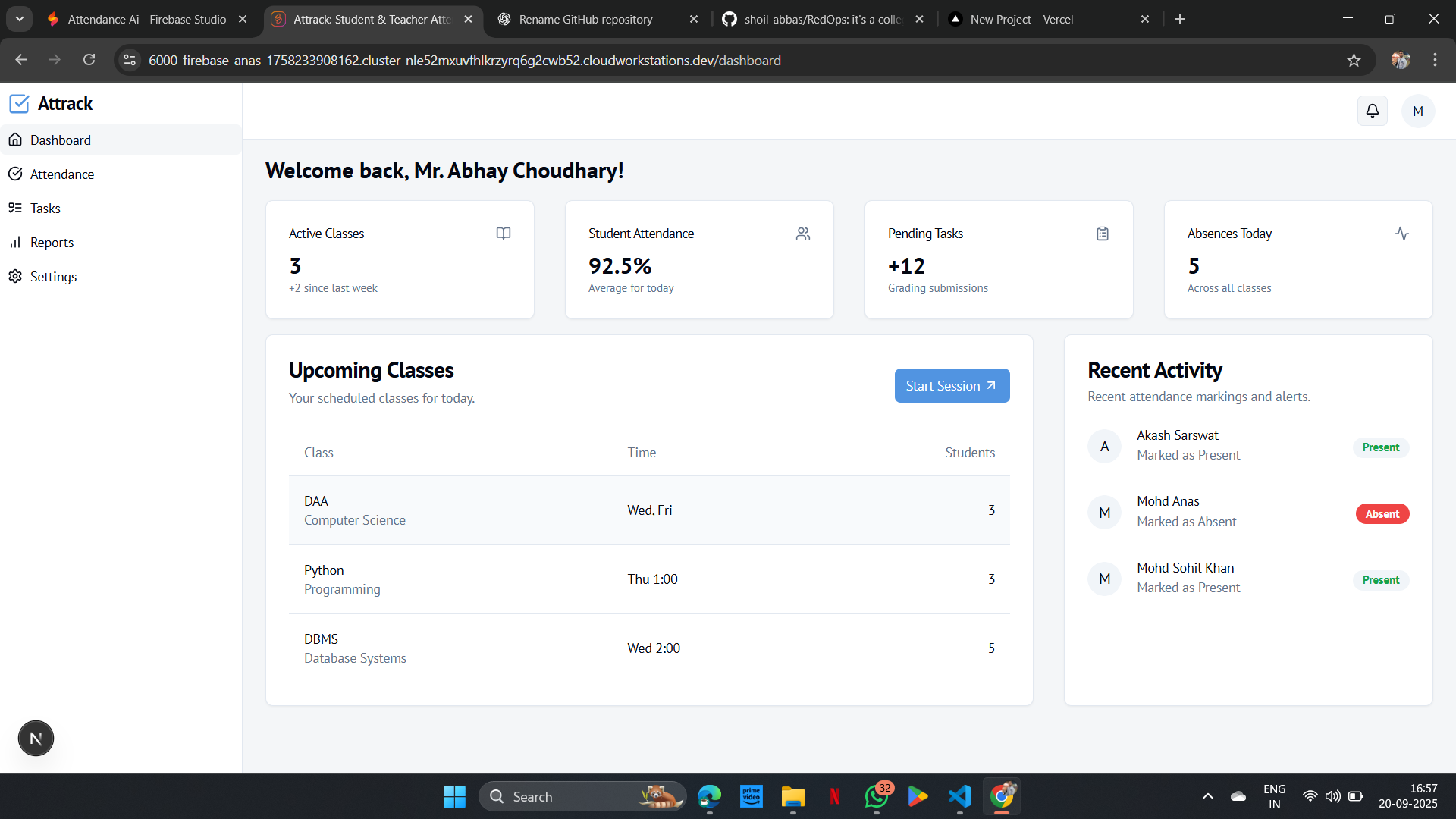.png)
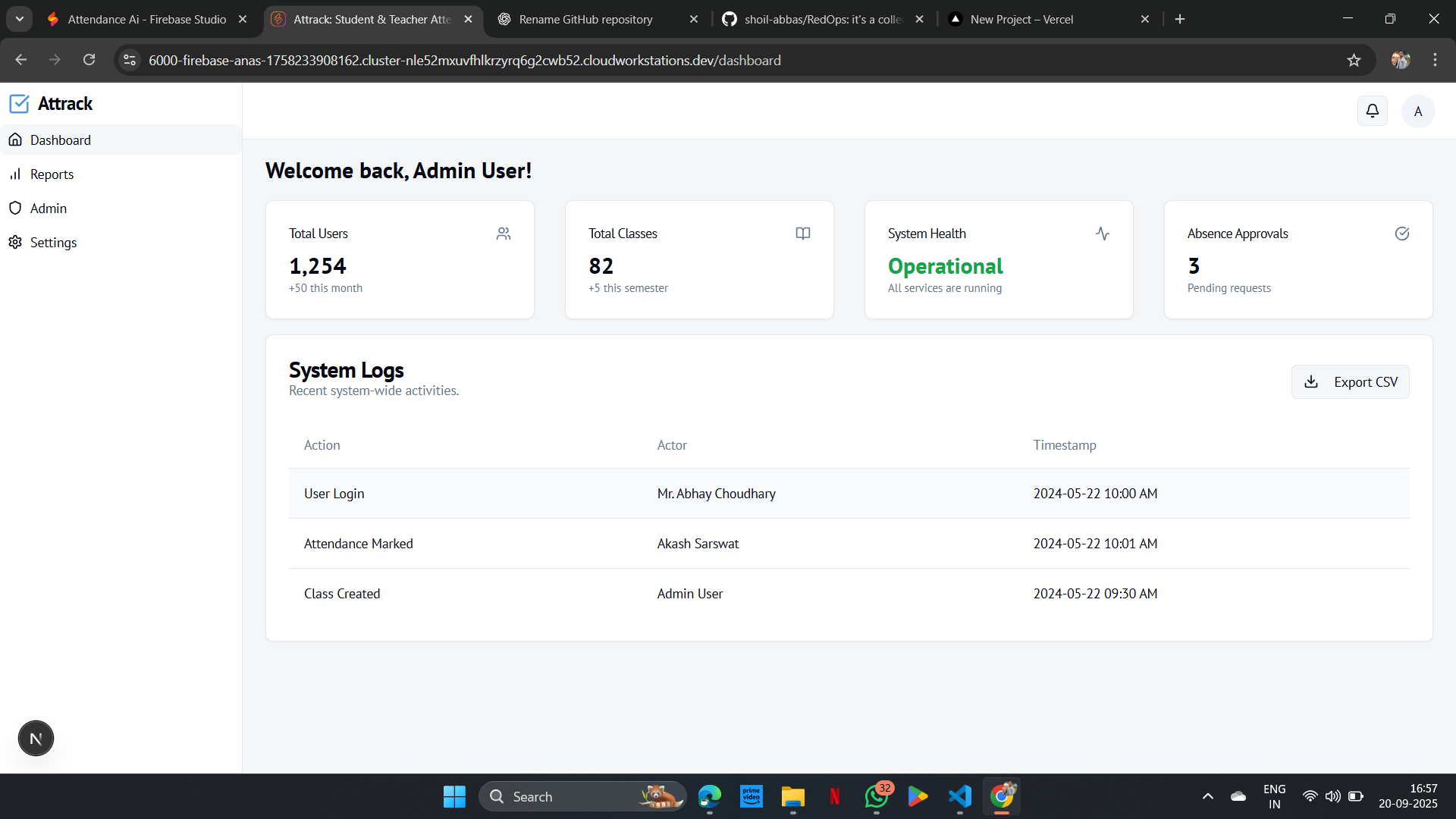.png)
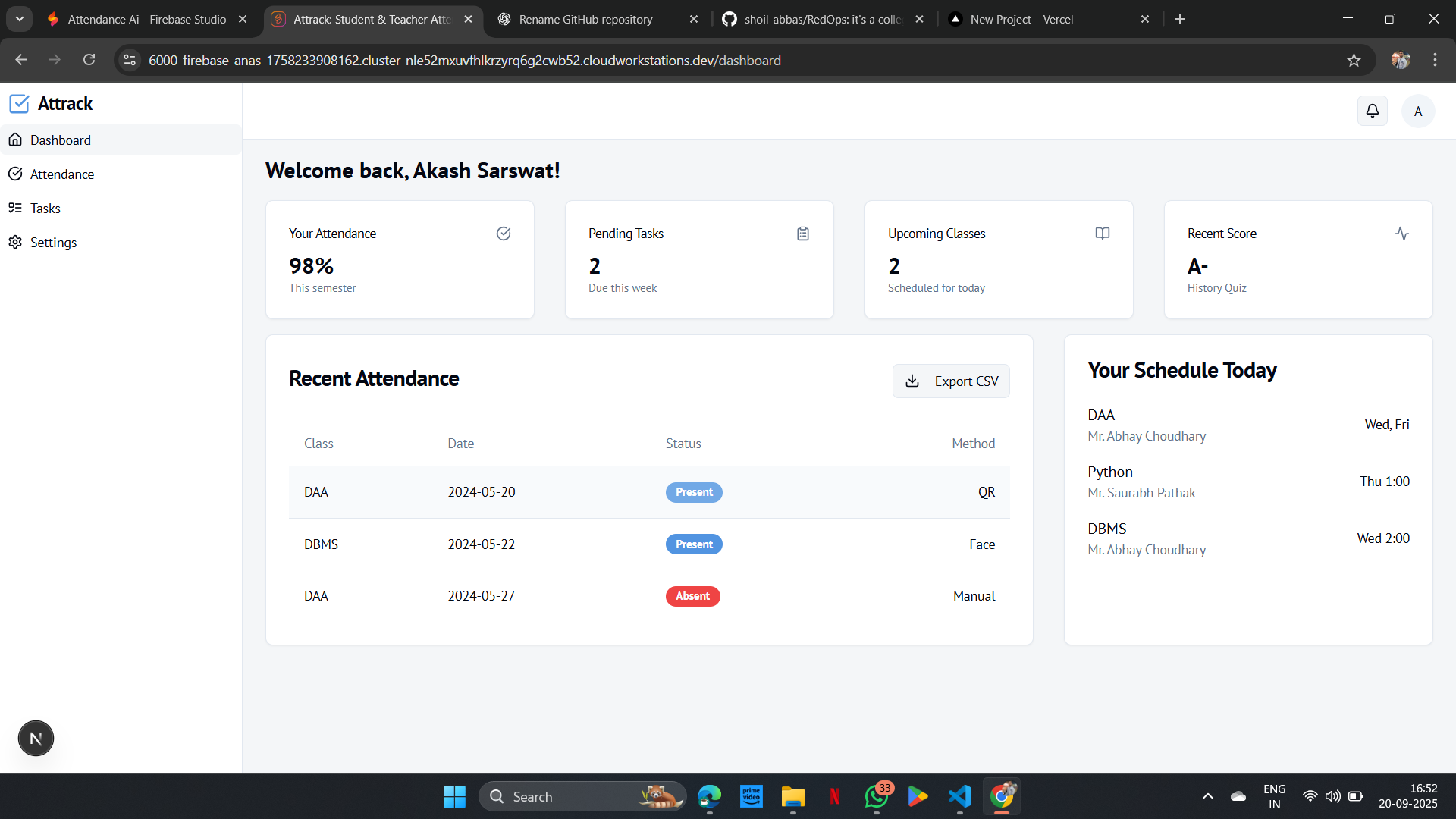.png)
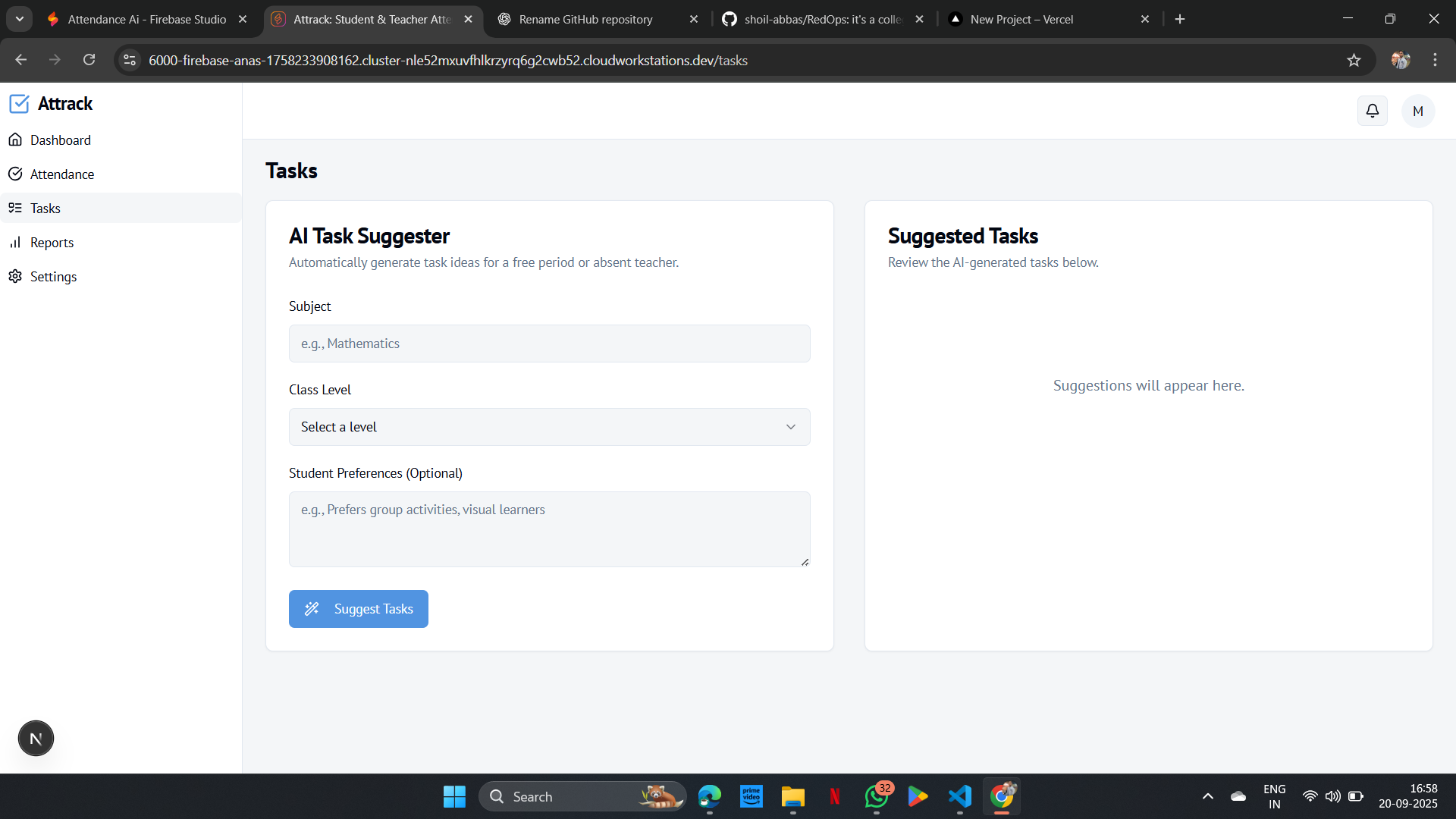.png)
.png)