RuleForge
Link to open source: https://github.com/Ishanb747/HackFest-2.0
Link to Live Project: https://rule-forge-front-end.vercel.app/scan-now
How RuleForge Works
Purpose: Automate compliance monitoring by converting unstructured policy PDFs into executable database queries that detect violations in real-time.
Three-Phase Pipeline
Phase 1 - RuleForge (Policy Interpretation)
Uses Docling to parse PDF documents and extract text
CrewAI agent (RuleArchitectAgent) interprets natural language policies
Converts unstructured rules into structured JSON with:
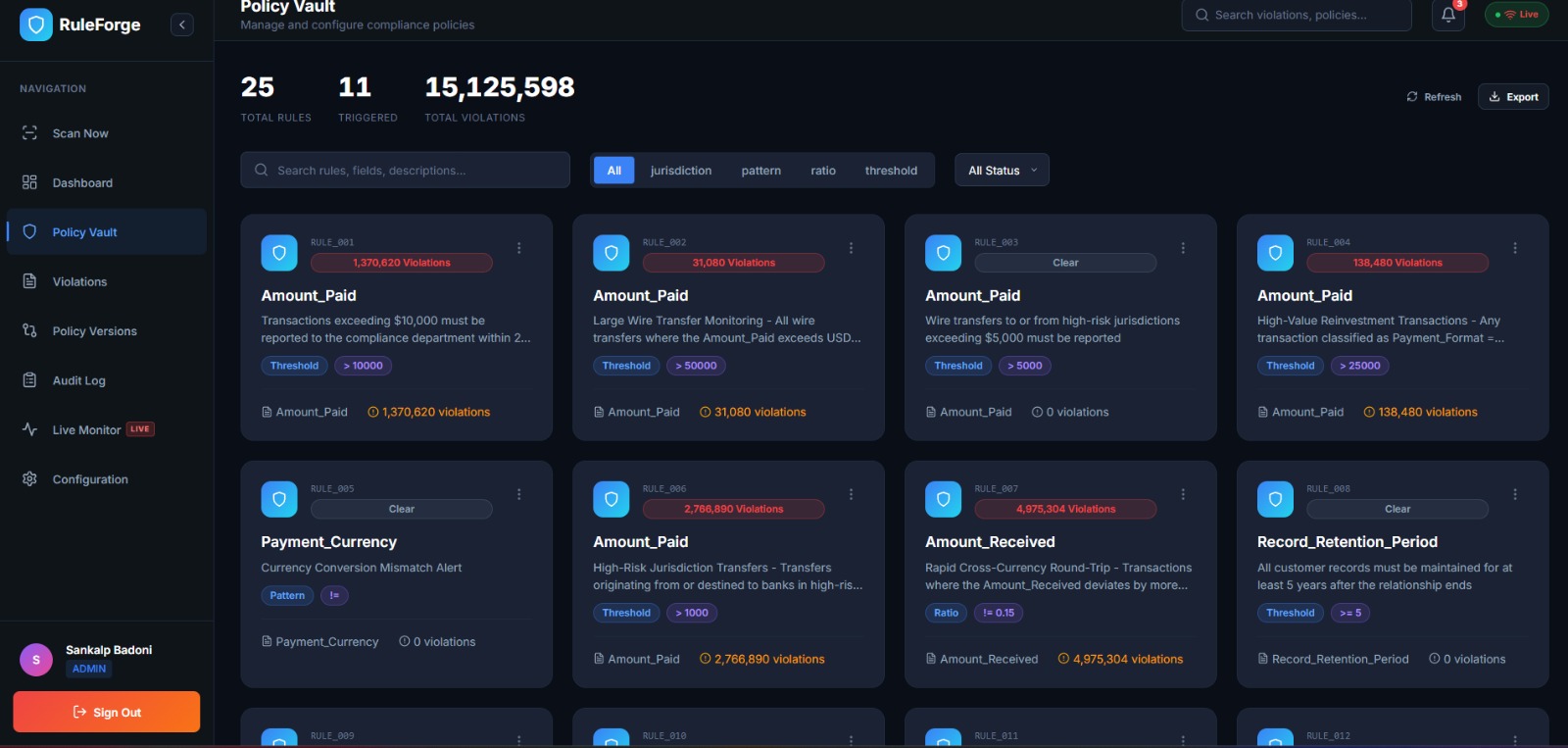
Rule ID, type, and description
Condition fields (e.g., "Amount_Paid")
Operators (>, <, =, IN)
Threshold values
SQL hints for query generation
Stores rules in policy_rules.json with version control
Phase 2 - SecureMonitor (Violation Detection)
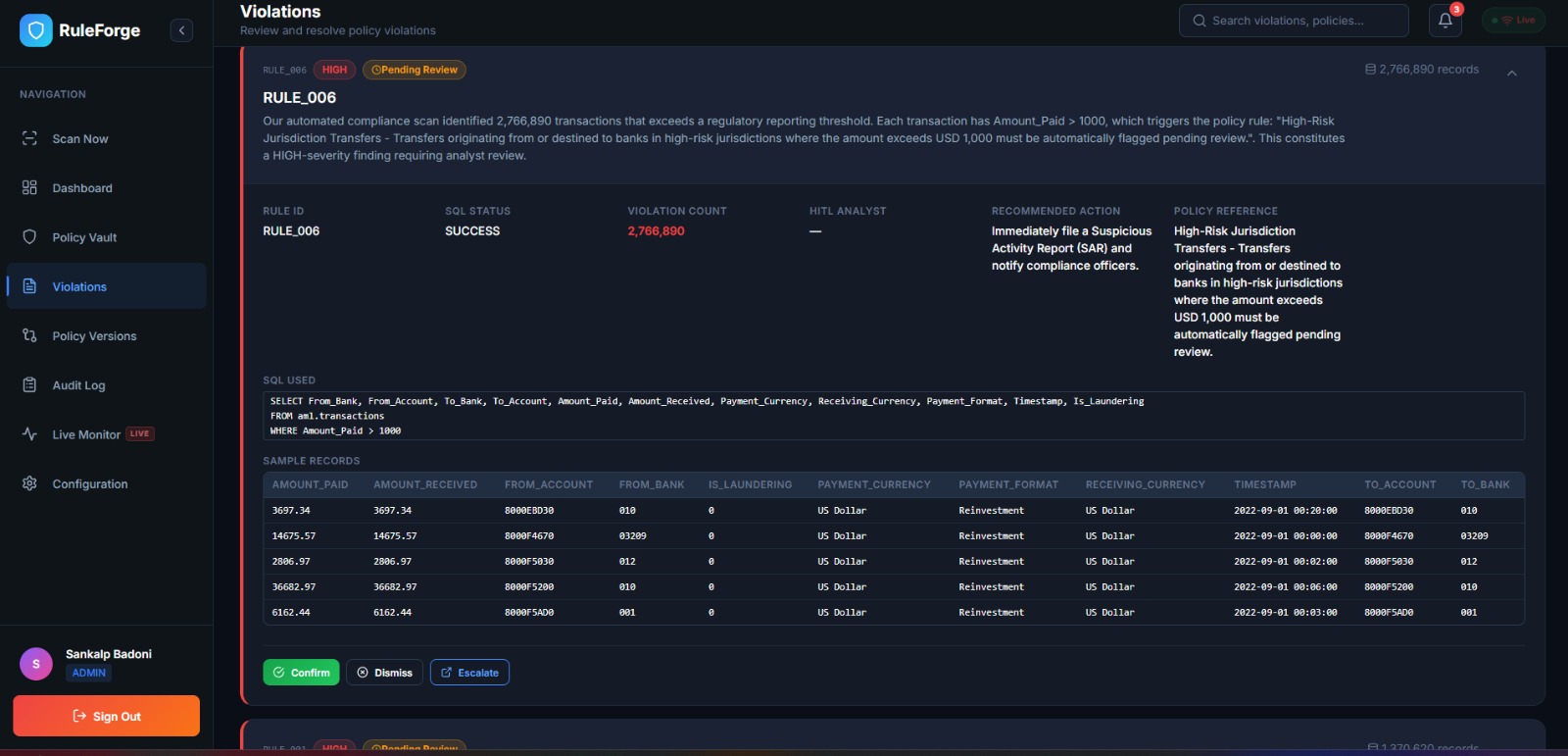
Deterministic SQL generator reads structured rules
Builds SELECT queries targeting DuckDB transaction database
SQL sandbox validates queries (SELECT-only, no DDL/DML)
Executes queries against transaction data
Outputs violation_report.json with:
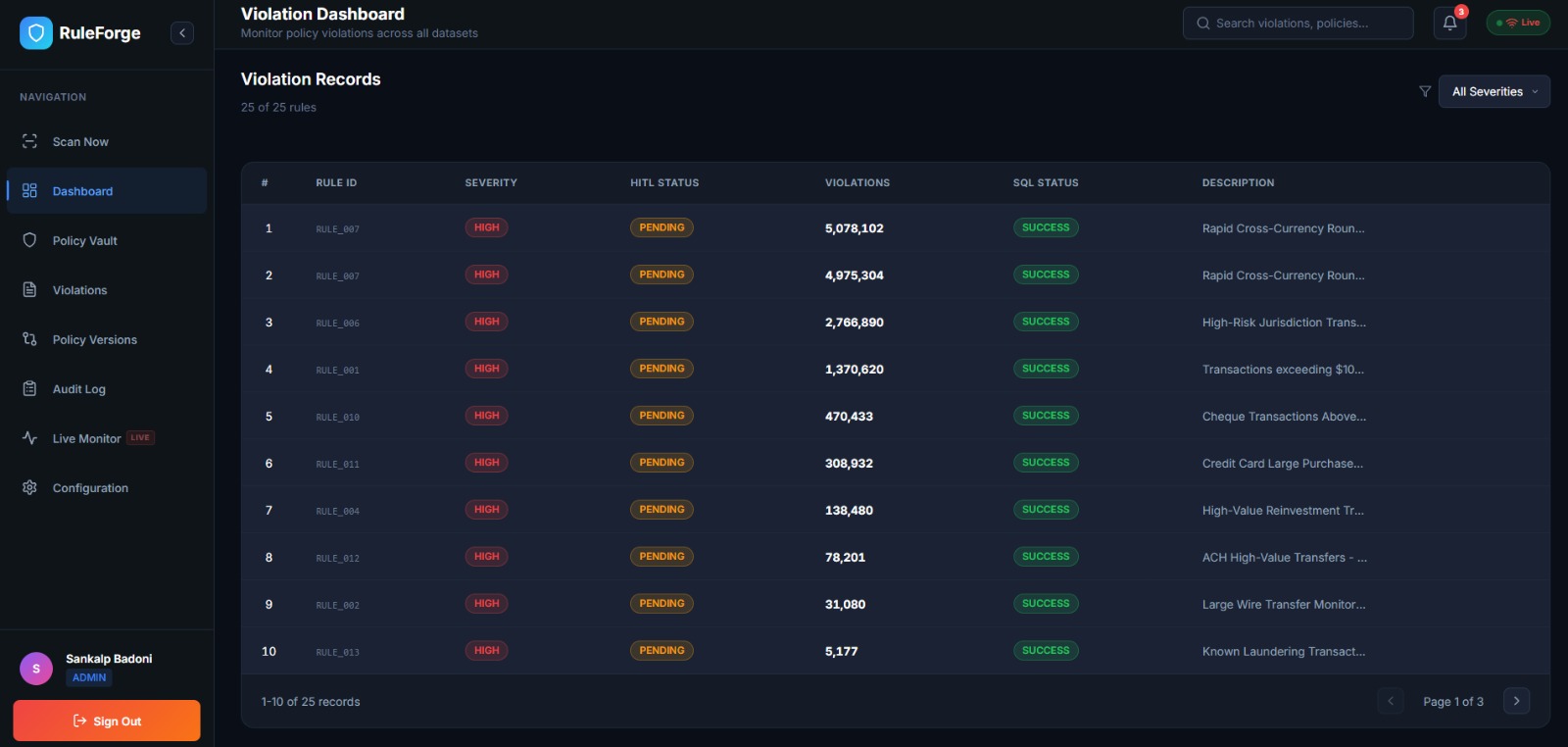
Violation counts per rule
Sample violating transactions
Query execution status
Phase 3 - Explainer (Human-Readable Alerts)
LLM agent converts technical violations into plain English
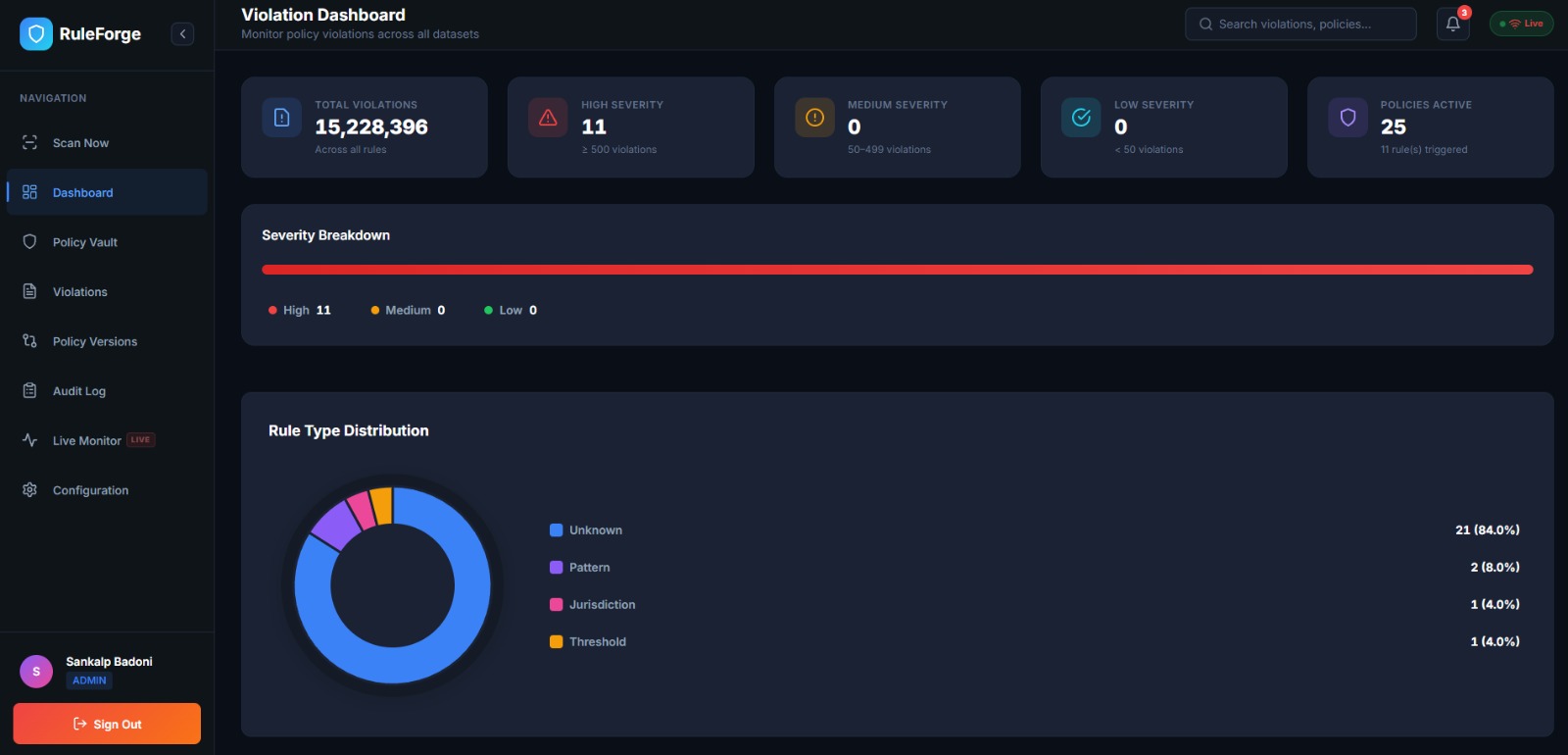
Generates risk levels (HIGH/MEDIUM/LOW/CLEAR)
Provides recommended actions and policy references
Creates explanations.json for stakeholder review
Key Features Addressing Goals
Transparency & Explainability
Every rule extraction is versioned and archived
SQL queries are visible and auditable
Immutable audit log tracks all decisions
Human-in-the-loop (HITL) interface for analyst review
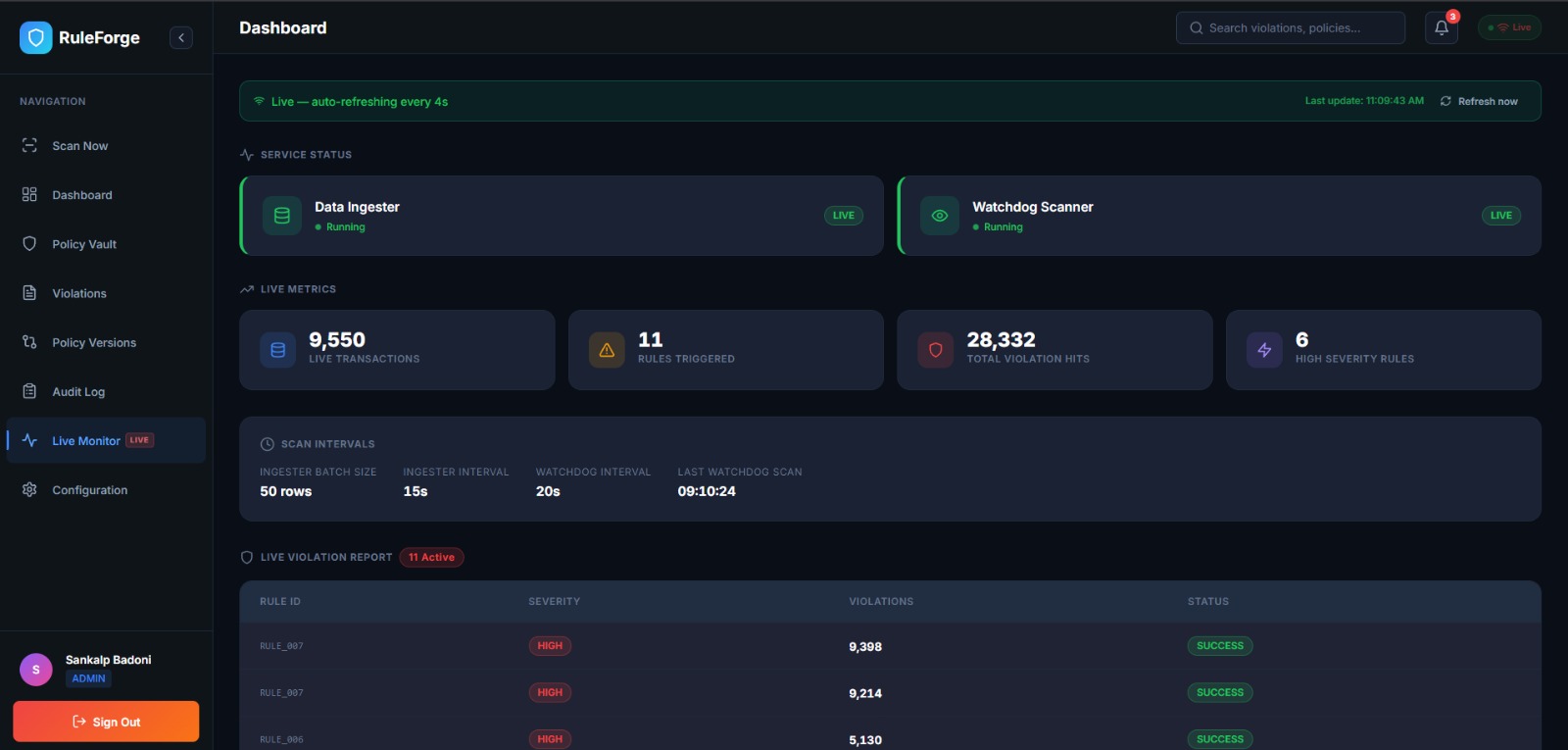
Real-Time Monitoring
ingester.py: Simulates live transaction stream
turgon_watchdog.py: Polls for new data and auto-detects violations
Live dashboard shows violations as they occur
Configurable polling intervals (default: 20s)
Scalability
DuckDB handles millions of transactions efficiently
Read-only connections prevent data corruption
Batch processing with configurable limits
Parallel rule evaluation
Fraud Risk Reduction
Detects suspicious patterns (e.g., round amounts, currency mismatches)
Flags high-risk transactions (>$10K, cash payments)
Identifies structuring attempts (amounts just below thresholds)
Regulatory Adherence
Version control tracks policy changes over time
Compliance reports exportable as JSON/CSV
Audit trail proves due diligence
HITL decisions logged with timestamps
Technical Stack
CrewAI: Multi-agent orchestration
Groq/LLM: Policy interpretation and explanation
DuckDB: Fast analytical queries on transaction data
Streamlit: Interactive dashboard with live monitoring
Docling: PDF parsing and structure extraction
This architecture transforms manual compliance (hours/days) into automated monitoring (seconds), while maintaining human oversight through the HITL interface and providing full audit trails for regulatory review.
This build was uploaded as a hackathon project